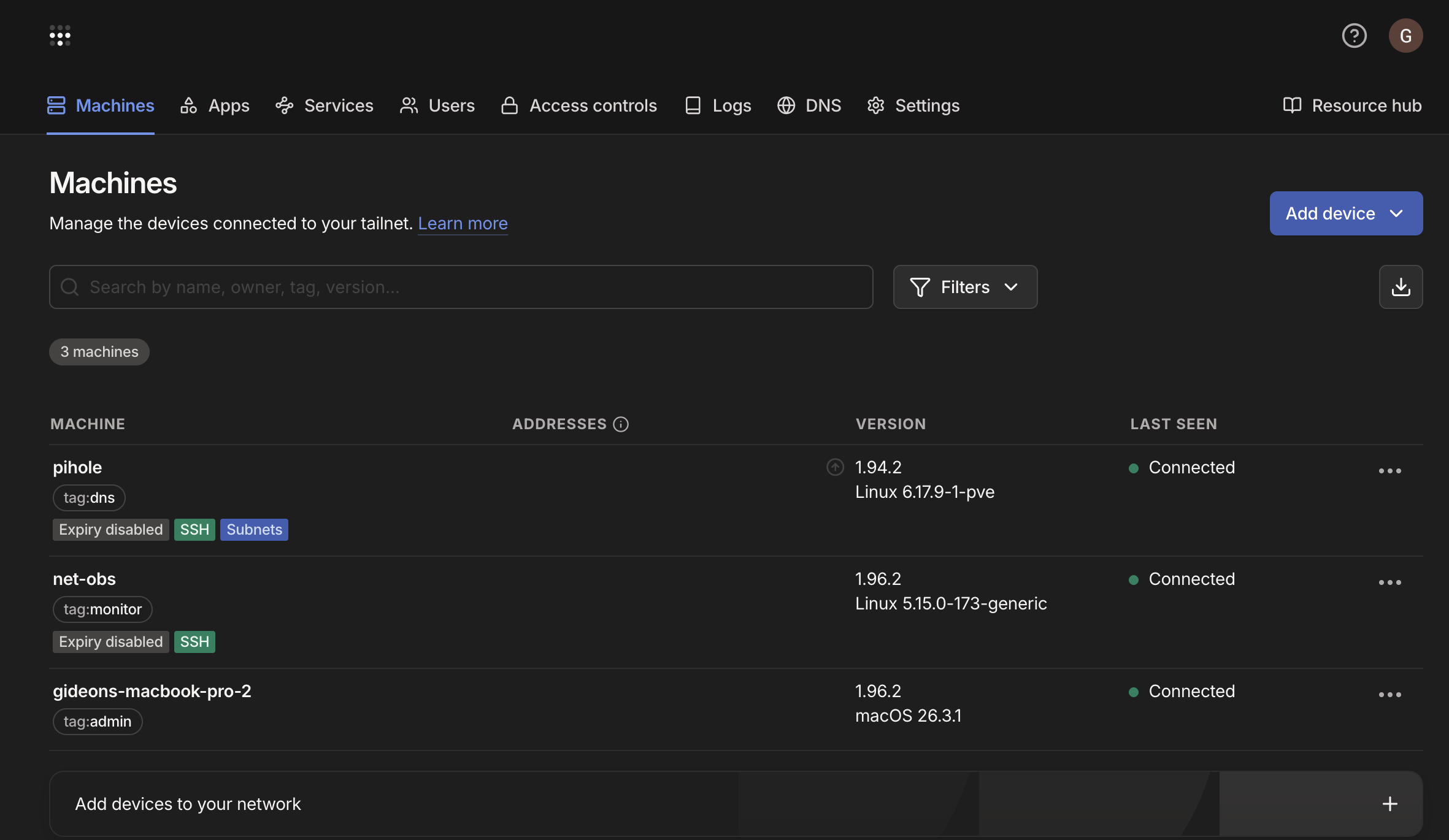
Tailscale Zero-Trust Access
Remote access to the platform without a traditional VPN. No open inbound ports, no static credentials, no implicit trust once “inside.” A WireGuard overlay provides identity-verified, policy-enforced access to internal services — and the upstream network never changed.
The problem with the old model
A traditional VPN wants an open inbound port, shared credentials, and trusts anything that makes it past the perimeter. For a lab that needs to be reachable from untrusted networks, that’s attack surface bought for convenience. The goal here was remote access with none of those tradeoffs.
Architecture
Every client and lab node runs Tailscale. Traffic from a remote client rides the WireGuard overlay, gets its identity verified and ACLs evaluated at connection time, then reaches internal services through a single subnet router.
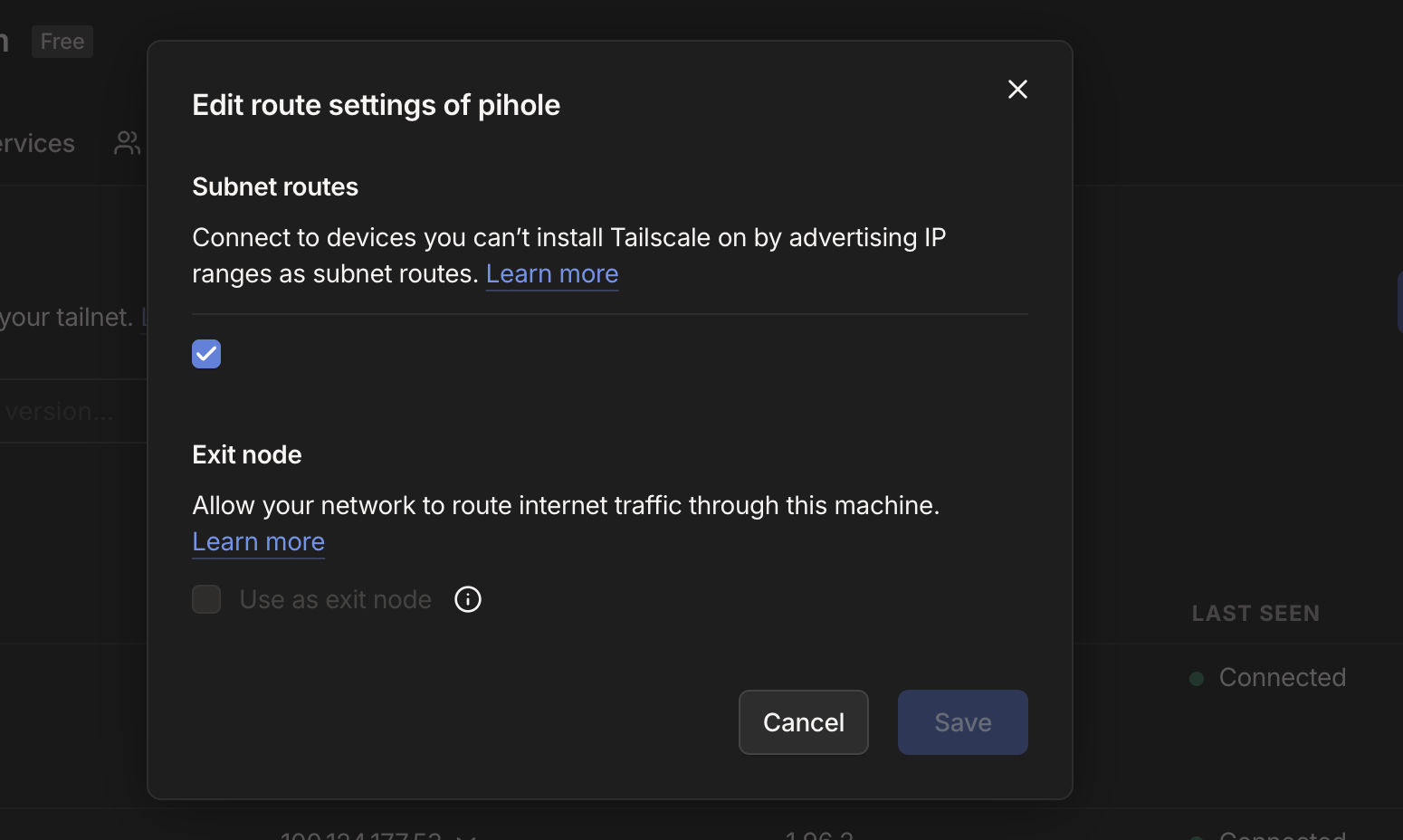
Pi-hole is that subnet router — it advertises the internal /24 and handles NAT, so enrolled clients reach LAN hosts by their real addresses without Tailscale on every box. It doubles as the DNS layer, which means every client resolves through Pi-hole’s filtering regardless of physical location.
Only traffic destined for the internal subnet crosses the overlay — subnet routing, not a full exit node. Lower latency, and a compromised node has a smaller blast radius.
Policy as code
Access control is deny-by-default and lives in a version-controlled ACL — not iptables rules scattered across hosts. Three tags, three tiers:
tag:admin — full subnet, all hosts, all ports.
tag:dns — Pi-hole port 53 only, nothing else.
tag:monitor — Grafana, Prometheus, and Alertmanager — and explicitly nothing else.
The ACL ships with test assertions: tag:dns is verified to reach port 53 and verified to be denied SSH and Grafana. Policy changes take effect across every node instantly, with no host-level config touched.
Key design decisions
No inbound ports. The edge firewall has nothing open. Every connection initiates outbound from the client through Tailscale’s coordination server — the internal network is never directly addressable from the internet.
Tags over firewall rules. Segmentation is identity-based and centralized. Adding a node or changing a tier is an ACL edit, not a sweep through per-host iptables.
Pi-hole as the single subnet router. Centralizes both subnet advertisement and DNS filtering on one lightweight node instead of spreading either across the fleet.
Roadmap
Private service publishing via `securebytes.net`, TLS termination through a Caddy reverse proxy, SSO via Entra ID, and multi-site subnet routing.
Stack